Visitor Location
Your location...
Confirm your location and select country flag.
Europe
- Latest Austria articles
- Latest Cyprus articles
- Latest Denmark articles
- Latest Estonia articles
- Latest France articles
- Latest Georgia articles
- Latest Germany articles
- Latest Greece articles
- Latest Hungary articles
- Latest Italy articles
- Latest Latvia articles
- Latest Liechtenstein articles
- Latest Luxembourg articles
- Latest Slovenia articles
- Latest Spain articles
- Latest Sweden articles
- Latest Switzerland articles
1 - What Visitors Are Particularly Interested In
2 - What Visitors Are Particularly Interested In
🇸🇪 Studio 65 - SVT - "Hur står det till med hemtjänsten?" 2024-11-07
🇸🇪 Region Skåne polisanmäler vårdbolag - “Oacceptabla brister”
🇸🇪 Brister i patientsäkerheten som lett till snabb uppsägning av avtalen.
🇸🇪 Palliativ vård - Midazolam + Morfin
🇸🇪 Palliativ vård - Midazolam + Morfin + Oxynorm + Gabapentin = Koma, Syrebrist, Hjärnskada, Död?
3 - What Visitors Are Particularly Interested In
🇸🇪 Vårdcentral i Höganäs "råkade missa" att man i 70 års åldern hade cancer.
🇸🇪 Tystnadskultur inom Hemtjänsten i Ängelholm.
🇸🇪 Brutal försämring av hemtjänstindex.
🇸🇪 Patientskadenämnden och IVO när hemvården inte blev bra? Turordningen kan vara avgörande.
🇸🇪 Höganäs Hemtjänst - Hantering av medicin.
🇸🇪 Avvikelser som inte är i enighet med gällande lagstiftning tydliggör.
🇸🇪 Övervakning av hemtjänst? Konkret exempel på vad som har hänt i samband med hemtjänst.
🇸🇪 Polisen varnar för falsk hemtjänst.
🇸🇪 Växling av läkemedelsfabrikat - Patientsäkerhetslagen 2010:659
4 - What Visitors Are Particularly Interested In
🇸🇪 Region Skåne - Analys av Journalutdrag. Fullgod syreupptagning över tid.
🇸🇪 Vårdtagare blir fast i den tillfälligt inhyrda sjukhussängen pga uppfällda fallskydd/ grindar.
🇸🇪 Hemtjänst Höganäs - Tänk på detta när du ska anlita Hemtjänst!
🇸🇪 Kommunal Hemtjänst - Leverantörens självinsikt och erkännande efter Socialstyrelsens mätning.
🇸🇪 Återupprepade likartade händelser inom ramen för medicinhantering inom hemtjänst beror inte på slumpen.
🇸🇪 Polisen misstänker brott - Tillslag mot hemtjänst 2025-03-11.
🇸🇪 Ställa diagnos innan medicinering eller medicinera innan diagnosställande?
Featured Articles - Karl-Johan Gyllenstorm

- Details
- Category: Karl-Johan Gyllenstorm
- By Karl-Johan Gyllenstorm
- Hits: 490
- SEO score for this article is: 74/ 100
- All rights reserved: The content is published with support from the freedom of expression constitution and the freedom of the press regulation © 2025.
- Longitude Latitude: -
- Geographical Area: Global
- Article subject: How i secure part of my Google account. How data functions and data commandoś are used by developers and server owners.
- Reading time: 2-5 min
- Age Target group is: Age 17-98
- The article contains: Digital security information
- XML synced to number of sitemaps: 23
- XML Synced: Synced with multi XML sitemaps
- .:
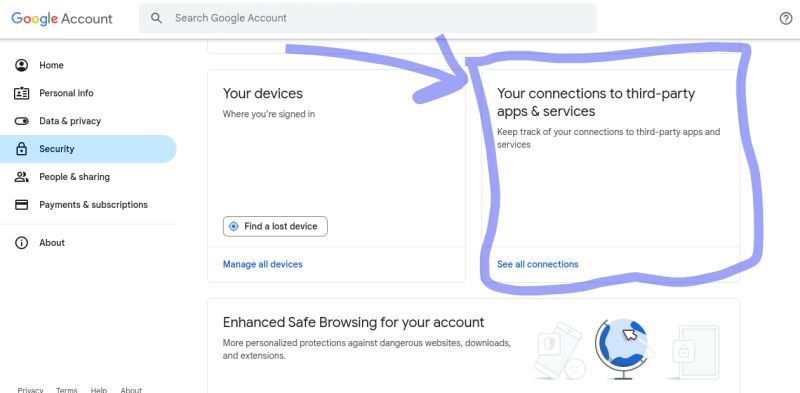
What permissions/ connections have you granted in your applications in your Google account?
*Regularly reviewing which applications are connected to third-party applications and services in my Google Accounts is something I do NOT renounce.
Generally, I keep my table completely clean. That is, I grant no connections/ permissions. If it is done, then it is only for the moment when the application is used. When I'm done, I remove all permissions immediately in the -> Google account.
Why does the application/ developer request permission/ connection to your:
Place
Phone call
Microphone
Camera
Etc....
What is the purpose?
The exchange.
What do you give and what do you get? "What do you buy what do you sell?"
Computer functions and computer commands in applications and on web pages.
Many people use the internet as a kind of playground where you click on anything at random without much thought. What one should be aware of when clicking on links, buttons, sending forms, verifying via e-mail, etc. is that there is most likely one or more data functions/data commands embedded in the link, which may consist of a button in an application or on a homepage.
Consent to the developer being allowed to use these data functions/ data commands is given by the user when he accepts the application's/ webpage's terms of use. Terms of use that can be very extensive and complicated and that most people never read.
In addition, some websites/ applications save user data.
User data such as sent through messages between users, information that users enter in comment fields, etc. If you do not want user information to be saved, then perhaps it is better, if possible, to send an email to the person to whom you are sending any form of information/ content.
A scary example of what I describe above could be a user connecting to the internet through Wifi connection to an application. When the user sends a message in application, the Wi-Fi network connection suddenly changes and the application used automatically gets access to the user's exact location.
Of course, several different data functions can be used by a developer in an application or on a web page - there are really no restrictions in this context.
It's all about what purpose the developer has with their software. And this can of course vary over time.
There are also applications that can be used in mobile phones that are developed to carry out several different data commands when an incoming phone call, e-mail, sms, notification etc. arrives. Often such an application is developed from "IF EVENTS", i.e. IF incoming phone calls from phone number 0000000000 "DO THIS", for example send a message to Contact with phone number 00000000000 and an email with the text "example" to the e-mail address @........ .
Concretely, one triggering data function triggers several different data commands either at the same time as the triggering first data function or after some time delay. This kind of computer technology is used a little everywhere, but in different kinds of packaging. For example, in the car industry, when a car owner has driven a certain number of miles, a service light comes on dashboard, when the fuel tank starts to run out, a light on the dashboard comes on, informing the car owner that it is time to refuel etc.
Data functions/ data commands are everywhere and it is good to be aware of how these work from several different aspects.
If you want to try intertwining different data commands, then you can try the service IFTTT. This gives you perspective on how the data command can be used on web pages.
This together with Ai, there are no limits anymore about what a data commando can do.
Some services require the user to connect to their service through their application.
This forces the user to use the application which is controlled by the developer and NOT the user itself.
To take this a step further, it is also the case that the data information that a user sends must pass several filters in the form of servers and/ or manual reviewś in applications before the information reaches the recipient. This means that the sender can never be completely sure that the information reaches the recipient and, IF it reaches the recipient, that the information is in original condition and nothing else?
If the application developer wants to cut you off completely then they can easily do it, if your phone operator wants to cut you off completely from incoming calls and SMS then they can easily do it.
Through data functions and automated data filtering, powerful results can be achieved (good or bad?). Play with the idea of what this could result in if a recruitment system uses this technology wrong/right, if a dating application uses the technology, social media applications, email client and more.
It could mean that only certain people that the developer or server owner has decided will get feedback on the information that the user sends. Whoever owns the application or data server is also the one who owns the power and has the ability to partially determine the success of others on the Internet. This fact is, of course, worrying, for example, for entrepreneurs who depend on the digital communication working flawlessly.
In this context, it matters less if you have the absolute latest and most modern mobile phone/ computer - it is still the server owner who has the power over how the data information is used. This may be part of the reason why some individuals do not reach any development. Because someone or some have decided to limit, cut off the individual from communication by using data filtering, data functions, data commandś (*how data is washed) in applications and in servers. Furthermore, imagine if a telephone mast in a certain city is owned by an investor who has the goal of taking control of an entire city......
Filtering out data from server/ database/ application can be done based on:
IP address
Telephone operator
Geographical location (country, city etc)
E-mail address
Email client
Phone number/ IMEI
Time (time, date)
And more.....
Do you trust data, should you trust data, can you trust data?
Other articles:
- Digital Marketing and Gliding Technique. Illogical Order Of Input Value In Google?
- Apps For Seo Purpose?
- This is how you increase the number of views on a YouTube video and make visitors stay longer on your website. The ultimate seo sauce!
- How does implementing advertising systems affect website seo?
- What is best? Linking to other "luxury cruisers in Monaco" content on the same web page or linking to content on an external website - SEO?
- To automate the Google Chrome browser in combination with a VPN accessory.
- 🔴 Region Skåne - Det är brister i patientsäkerheten som lett till snabb uppsägning av avtalen. Om patientsäkerheten inte uppfylls är det skäl att häva avtalet.

Karl-Johan Gyllenstorm is an SEO expert, marketing writer, he is certified in digital marketing by Google Digital Academy 2020. Karl-Johan is also known as “Gyllenstorm.”
Karl-Johan Gyllenstorm was born in 1976 on June 21 in Mölle. Has knowledge in internet marketing with a focus on search engine optimization (SEO). He has expertise in online personal brand strategy and expansion, market analysis, affiliate marketing web automation, extravagant search engine optimization methods. Other relevant knowledge and university studies can be found in the subjects of data analysis and statistics as well as in radiology and image analysis. He got part of his breakthrough when he started his craft company in 2008. Karl-Johan has a patent for the name "Gyllenstorm". Karl-Johan Gyllenstorm has worked as a team base, project manager and site manager in previous professional activities. Gyllenstorm is one of the arms of the House of Knights.
Karl-Johan Gyllenstormś digital books.
Karl-Johan has over 16 years of experience in digital marketing.
The digital marketing journey started in 2008. Karl-Johanś first digital marketing project was a website for his painting business.The website was built in the Joomla system and dominated on relevant Top keywords in the painting industry. He now writes articles about marketing and search engine optimization in the Joomla system and shares his knowledge with the whole world.
Learn more about Karl-Johan Gyllenstorm.
Age: 48
Weight: 106 kg
Length: 188 cm
Shoe Size: 46
Hair color: Brown
Body type: Athletic
Instagram: gyllenstorm_kj
Twitter: gyllenstorm_kj
Medium: kgyllenstorm

- Details
- Category: Karl-Johan Gyllenstorm
- By Karl-Johan Gyllenstorm
- Hits: 5501
- SEO score for this article is: 70/ 100
- All rights reserved: The content is published with support from the freedom of expression constitution and the freedom of the press regulation © 2024.
- Longitude Latitude: Longitude 12.85339, Latitude 56.42689
- Geographical Area: Båstad
- Article subject: WiFi Network Secure - Email validation - Email security
- Reading time: 5-10 min
- Age Target group is: Age 17-79
- The article contains: Wifi security information and email security information
- XML synced to number of sitemaps: 23
- XML Synced: Synced with multi XML sitemaps
- .:
I use Wifi and over time have had imminent network WiFi problems and all that that has entailed. From time to time I have also noticed that my e-mail did not work correctly and behaved strangely in several different ways.
There are solutions to most problems and answers to errors. These solutions and answers I will share with you as a reader with the aim of helping you not to be exposed to the same problem that I have had to share.
I'll start by going straight to the point and want to say right now that if you don't use Wifi or e-mail then you have no use for what will appear in this article. However, if you use Wifi and e-mail then you must read what appears below.
Wifi is good but there are flaws in security.
These flaws open doors for hackers and criminals. Security flaws in Wifi networks allow hackers to gain full visibility into what you do on the internet and who wants that to happen? This is precisely why you should be extra careful with open Wi-Fi networks in public places, etc. If you use public Wifi networks, do not carry out banking, payments, etc.
There are different security classes in Wifi WPA, WPA2, WPA3, etc. with associated detailed settings that are made in the user's router. These detailed settings are very important, they are just as important as using the right security class WPA2, WPA3 on the Wifi network.
I'm not going to go into details about settings in the Wifi router, but I can mention that WPA2, WPA3 are what you should use from a security perspective.
In my research, I have received one thing that is very clear, and that is that the password to the WiFi network, to the router, and the SSID is objective.
Hackers use complex tools to hack into WIfi networks and part of the hacking process is to crack passwords, usernames. Bad passwords and poor Wi-Fi security make it very easy for hackers to connect to your Wi-Fi network, it only takes about ten seconds for a hacker to get into a Wi-Fi network that has poor security. If you use Wifi, then you should care about this and make sure your Wifi is secure!
So how do hackers hack into Wifi networks?
There are several different methods that they use, somewhat depending on where the victim is.
-
Man in the middle Wifi hackning is a technology that can be used in restaurants, cafes, hotels, etc.
-
Another more complex and brutal hack is WiFi Pineapple Enterprise.
-
Hacking using “Flipper” hardware. Flipper is a small battery-powered device that hackers place near their victim. It can be, for example, in a basement under the victim's home, in a plastic bag well hidden in a garden bush outside the victim's home/office, etc.
-
StingRayś
These are just a few examples. I am far from a network expert or an IT security expert, but these are examples. If you want to learn more about these, I advise you to watch YouTube - there you can get full insight.
So concretely, we can say that your Wifi passwords and router passwords are set against the hacker's software which is designed specifically to crack passwords and to hack Wifi networks, take control of Wifi networks.
You probably already understand that a password of a few letters and numbers is far from enough to prevent the hacker's software from cracking your passwords. In general, we can say that the longer your password is and the more irregular characters and symbols that are included in the password, the more secure it is. I recommend you to use a password that contains 64 irregular characters consisting of letters, numbers, symbols. Do not use word combinations. And do not save your password on your devices!
Often it can be experienced as difficult and boring to have to familiarize yourself with Wifi security and having to change basic settings in the router/software. But hopefully this is something you do once and after that your Wifi is safe! You can relax and not have to feel any stress that your Wifi is insecure and monitored by hackers/criminals. What a feeling ;)?
When you have set up your Wifi network by changing the basic SSID, changing the default password to your own which is 64 characters and setting other parameters in the Wifi router, the next step follows.
This is also very important to understand and to implement. Hackers who use Wifi Pineapple Enterprise Technology can see everything that happens in the hacked Wifi network, but if you use a secure VPN connection then they cannot see what you are doing on your Wifi network. This is because the VPN IP address is an intermediate element between you and the hacker. So install VPN in your device if you don't already have it. Don't choose the first best VPN provider on the Google Chrome Store or on Google Play, choose one that has received good ratings and is not related to an inappropriate country. Proton VPN is a variant that many feel safe with.
What you should take into account in the secure calculations is that the VPN provider can see what you do on the internet. The same with your internet provider and with the Police. And this is usually not a problem as, for example, the Police can see which web pages you surf on if you are not a criminal.
If you use a Google account, follow their security information when registering an account. Google is at the forefront of user security.
Set your browser (Chrome) to enhanced security, set so that cookies are deleted when the website is closed. Set your mobile or computer's DNS to Google DNS or to Quad DNS (Google DNS is recommended).
Use a good virus protection that is safe, Avast, AVG are examples of such and that are also free.
Check that your applications are up to date, check that your software in your computer is up to date. If you use Google Chrome, click on the settings tab and go to the Security tab. Check which apps are installed on your mobile phone, if there are any unknown ones that look suspicious choose to uninstall them! Restore your devices to their factory settings, this eliminates the risk of any malware having a long-term effect on you/ your device.
If you're as geeky as I am when it comes to security, then you build your own Chrome Extensions to strengthen your browser's security.
Nearby Sensors can be found in all Mobile Phones as well as in some other devices. Through my Chrome accessory, I can see which ones, should a new device show up in combination with my Wifi Network Monitor giving me an indication that the network's IP has changed, then this reinforces the credibility that active hacking is being carried out.
Wifi network monitor shows and alerts me if my *network IP changes.
If it changes then it is an indication that the network is being manipulated and in such a case I can see which IP is related to the manipulation of my WiFi network.
This was a little basic about Wifi security. I hope it can add something to you that will make you have a more secure Wifi network. And again, you should care about the security of your Wifi network.
How many Wifi networks are hacked?
Statistics show that 1 in 16 Wi-Fi networks are hacked due to bad passwords or bad security settings in the router or in the user device. According to measurements, 79% of home Wi-Fi owners have weak passwords, which exposes users to security risks.
If your IP address changes, what do you do?
Firstly, it does not have to mean that your Wifi is hacked if your IP address changes. Internet providers sometimes change users' IP addresses, for example if a user turns off their devices and turns them on again, then the IP address can be changed. By using my Wifi Network Monitor Google Chrome Extension, you can see if the IP address changes. If it changes, copy the new IP address and do a search on it in Who is. Paste the new ip address in Who is and see if the new ip address is provided by the same internet provider or not. If it is the same, then you can be calm.
If it is not the same internet provider, change the password and SSID and check all security settings in your router and in your user devices / computer / mobile / tablet. And do not forget to update all your devices.
Further to e mail security.
In general, I only recommend Gmail as a secure email.
I'm not going to go into more detail about why, but Gmail has some security parameters that some other email providers don't have.
If you want to check the credibility of an email if you are a Gmail user, do the following:
-
Open the current email - (don't click on any links) and make sure you have your VPN on / activated. In some emails there is a tracking code that has the task of logging the recipient's IP, with the VPN turned on the IP for the VPN is displayed and not your real IP. Hackers are interested in IP, so always mask your IP.
-
Click on the 3 small round dots in the email at the top right.
-
Select show original.
-
Look at the parameters SPF, DKIM, DMARK so that they all have PASS.
-
Check that ARC matches with DKIM, i.e. that they have the same email domain. If they do not have the same email domain then you should be skeptical of the email, likewise if it is a subdomain.
Personally, I never take chances, with that said, either PASS is shown on all parameters and ARC matches with DKIM or it doesn't. If not then I discard the email and classify it as junk! Furthermore, for example, if the domain shows that the email is from company x.com, signed in the email signature by first and last name, and when checked, it turns out that first and last name work for company y.com, then this indicates that the email is classified as a scam. Again, look for common denominators in the email that either prove that everything is ok or that it is SCAM. As a starting point, you use the SPF, DKIM, DMARC and ARC parameters to perform a quick security check of your email.
If you want to check a domain then you can do this via Who.is. There you can get dates, owners and more.
This was a bit of basic security around Wifi and e-mail.
If hackers launch an overload attack (Dos attack) on your router after you have implemented proper security settings, the router will most likely shut down. But you can feel safe in the fact that in the event of such an attack, the hacker will not be able to access your Wi-Fi password and your router password. Consequences of an overload attack (Dos attack) against a Wifi router are often short-lived and can be solved by the user turning off the router for a few minutes and then turning it on again to connect to the internet. *Use Wifi channel 1,6 or 11.
That's all, hope the information added something that can lead to improvement when doing seo and digital marketing from Wifi network? Oh one more thing, turn off Wifi and Bluetooth when you don't use it. Wifi hacking is often done by someone nearby, be aware of who is nearby when your Wifi stops working. If the same person is around every time it happens then this could be the potential hacker. Hackers can also plant computers nearby and remotely connect to these to hack Wifi networks through software programs in the planted computer, e.g. Team Viewer 7, Anydesk etc.
Other articles:
- My WiFi Network Monitor Extension for Google Chrome Browser?
- Network Analysis
- Advanced Adblocker Extension for Google Chrome Browser
- My Auto Cache Cleaner for Google Chrome Browser?
- Email Pixel Trackerś - Measurement and Conversion Rate (in London?).
- User data a part of the digital marketing analysis and product development. “The user wanted one thing and got it plus lots of other things that were not originally requested, and payed for it?”
- Personal WiFi Password Generator With Strong Encryption
- A "Password Generator" that make it easy for me to generate my passwords for my own needś.
- What is a "Password Strength Checker" and how do i use it?

Karl-Johan Gyllenstorm is an SEO expert, marketing writer, he is certified in digital marketing by Google Digital Academy 2020. Karl-Johan is also known as “Gyllenstorm.”

Karl-Johan Gyllenstorm was born in 1976 on June 21 in Mölle. Has knowledge in internet marketing with a focus on search engine optimization (SEO). He has expertise in online personal brand strategy and expansion, market analysis, affiliate marketing web automation, extravagant search engine optimization methods. Other relevant knowledge and university studies can be found in the subjects of data analysis and statistics as well as in radiology and image analysis. He got part of his breakthrough when he started his craft company in 2008. Karl-Johan has a patent for the name "Gyllenstorm". Karl-Johan Gyllenstorm has worked as a team base, project manager and site manager in previous professional activities. Gyllenstorm is one of the arms of the House of Knights.
Karl-Johan Gyllenstormś digital books.
Karl-Johan has over 16 years of experience in digital marketing.
The digital marketing journey started in 2008. Karl-Johanś first digital marketing project was a website for his painting business.The website was built in the Joomla system and dominated on relevant Top keywords in the painting industry. He now writes articles about marketing and search engine optimization in the Joomla system and shares his knowledge with the whole world.
Learn more about Karl-Johan Gyllenstorm.
Age: 48
Weight: 106 kg
Length: 188 cm
Shoe Size: 46
Hair color: Brown
Body type: Athletic
Instagram: gyllenstorm_kj
Twitter: gyllenstorm_kj
Medium: kgyllenstorm
Contact:

- Details
- Category: Karl-Johan Gyllenstorm
- By Karl-Johan Gyllenstorm
- Hits: 5861
- SEO score for this article is: 89/ 100
- All rights reserved: The content is published with support from the freedom of expression constitution and the freedom of the press regulation © 2024.
- Longitude Latitude: -
- Geographical Area: Global
- Article subject: Traffic flow
- Reading time: 2-4 min
- Age Target group is: Age 15-70
- The article contains: Digital marketing information
- XML synced to number of sitemaps: 23
- XML Synced: Synced with multi XML sitemaps
How can you quickly determine the traffic flow on a website and determine if the website is suitable to put energy on from an online marketer's perspective?
Should you spend your time on the website or not?
Doing a quick analysis of the traffic flow on a website gives you answers on whether you should spend time posting links and content on the website or not.
Over 500,000 web pages are created every day.
Where should you who are active in online marketing put your focus?
Focus should be placed on pages where there is a high flow of traffic.
-
Pages that are given are of course the largest social media channels for social media marketing. Social media marketing is just one part of the overall online marketing.
-
Other elements are to publish links and content on forums and in blogs etc.
-
An online marketer should be able to quickly determine if the forum or blog is worth putting energy into - in short, if the forum or blog has a sufficiently large traffic flow.
To determine this, online marketers use various analytics tools and browser extensions.
The tool used is a Chrome extension and is completely free to use. If you want to know more about the tool click here.
Conclusion:
This article lists statistics obtained through a free browser extension used in Google Chrome. The tool is popular among online marketers 2024 because it helps the online marketer to determine if the website, forum, blog has a sufficiently large traffic flow. Do you post on the right blogs, forums? *If the social media, forum, blog does not give you enough traffic, put your focus on other sites that are better. Use the tool recommended in this article.
Other articles:
- Social Media Timing
- Wants their content to be visible 🇱🇺 Marketing Luxembourg
- Reuse and modify content to achieve SEO 🇲🇨 Monaco 🇨🇭 Switzerland
- Google Dance SEO affect in Monaco Online Marketing - Karl-Johan Gyllenstorm
- Digital marketing strategy 🇱🇮 Liechtenstein/ 🇲🇨 Monaco/ 🇧🇪 Belgium/ 🇱🇺 Luxembourg Karl-Johan Gyllenstorm
- Geographically linked to Gyllenstormstraße in 🇦🇹 Austria - Karl-Johan Gyllenstorm.

Karl-Johan Gyllenstorm is an SEO expert, marketing writer, he is certified in digital marketing by Google Digital Academy 2020. Karl-Johan is also known as “Gyllenstorm.”

Karl-Johan Gyllenstorm was born in 1976 on June 21 in Mölle. Has knowledge in internet marketing with a focus on search engine optimization (SEO). He has expertise in online personal brand strategy and expansion, market analysis, affiliate marketing web automation, extravagant search engine optimization methods. Other relevant knowledge and university studies can be found in the subjects of data analysis and statistics as well as in radiology and image analysis. He got part of his breakthrough when he started his craft company in 2008. Karl-Johan has a patent for the name "Gyllenstorm". Karl-Johan Gyllenstorm has worked as a team base, project manager and site manager in previous professional activities. Gyllenstorm is one of the arms of the House of Knights.
Karl-Johan Gyllenstormś digital books.
Karl-Johan has over 16 years of experience in digital marketing.
The digital marketing journey started in 2008. Karl-Johanś first digital marketing project was a website for his painting business.The website was built in the Joomla system and dominated on relevant Top keywords in the painting industry. He now writes articles about marketing and search engine optimization in the Joomla system and shares his knowledge with the whole world.
Learn more about Karl-Johan Gyllenstorm.
Age: 48
Weight: 106 kg
Length: 188 cm
Shoe Size: 46
Hair color: Brown
Body type: Athletic
Instagram: gyllenstorm_kj
Twitter: gyllenstorm_kj
Medium: kgyllenstorm
Contact:

- Details
- Category: Karl-Johan Gyllenstorm
- By Karl-Johan Gyllenstorm
- Hits: 1772
- SEO score for this article is: 45/ 100
- All rights reserved: The content is published with support from the freedom of expression constitution and the freedom of the press regulation © 2024.
- Longitude Latitude: Location BÅSTAD Latitude 56.42689000 Longitude 12.85339000
- Geographical Area: Båstad
- Article subject: SEO
- Reading time: 2-5 min
- Age Target group is: Age 20-70
- The article contains: Digital marketing information
- XML synced to number of sitemaps: 23
- XML Synced: Synced with multi XML sitemaps
- .:
The choice of path is simple when it comes to SEO.
Where the audience is there are also openings to build SEO and drive traffic to web pages. Writing an article in a blog can of course add something positive in terms of search engine optimization but then it must be in a blog that is established and has a steady stream of visitors/readers every day. Otherwise, online forums and online groups such as can be found on Linkedin and Meta are advocated. There must be some form of strategy and clarity when creating seo content, it's about building trust with Google.

Karl-Johan Gyllenstorm is an SEO expert, marketing writer, he is certified in digital marketing by Google Digital Academy 2020. Karl-Johan is also known as “Gyllenstorm.”
Karl-Johan Gyllenstorm was born in 1976 on June 21 in Mölle. Has knowledge in internet marketing with a focus on search engine optimization (SEO). He has expertise in online personal brand strategy and expansion, market analysis, affiliate marketing web automation, extravagant search engine optimization methods. Other relevant knowledge and university studies can be found in the subjects of data analysis and statistics as well as in radiology and image analysis. He got part of his breakthrough when he started his craft company in 2008. Karl-Johan has a patent for the name "Gyllenstorm". Karl-Johan Gyllenstorm has worked as a team base, project manager and site manager in previous professional activities. Gyllenstorm is one of the arms of the House of Knights.
Karl-Johan Gyllenstormś digital books.
Karl-Johan has over 16 years of experience in digital marketing.
The digital marketing journey started in 2008. Karl-Johanś first digital marketing project was a website for his painting business.The website was built in the Joomla system and dominated on relevant Top keywords in the painting industry. He now writes articles about marketing and search engine optimization in the Joomla system and shares his knowledge with the whole world.
Learn more about Karl-Johan Gyllenstorm.
Age: 48
Weight: 106 kg
Length: 188 cm
Shoe Size: 46
Hair color: Brown
Body type: Athletic
Instagram: gyllenstorm_kj
Twitter: gyllenstorm_kj
Medium: kgyllenstorm

- Details
- Category: Karl-Johan Gyllenstorm
- By Karl-Johan Gyllenstorm
- Hits: 1779
- SEO score for this article is: 69/ 100
- All rights reserved: The content is published with support from the freedom of expression constitution and the freedom of the press regulation © 2024.
- Longitude Latitude: -
- Geographical Area: Global
- Article subject: GNU development
- Reading time: 5 min
- Age Target group is: Age 20-70
- The article contains: Software development
- XML synced to number of sitemaps: 23
- XML Synced: Synced with multi XML sitemaps
Karl-Johan Gyllenstorm in 🇸🇪 Båstad has developed several different free GNU extensions that have largely had the same purpose.
To improve SEO and drive traffic to landing pages. Some extensions have been embedded on web pages along with the Google Bot Tag index if embed. The idea has been simple, says Karl-Johan Gyllenstorm. By giving away software, traffic and improvement in search engines has been achieved. To a large extent, it is the merit of the users. Some of the software is currently disabled, but some are still active and can be seen here.

Karl-Johan Gyllenstorm is an SEO expert, marketing writer, he is certified in digital marketing by Google Digital Academy 2020. Karl-Johan is also known as “Gyllenstorm.”
Karl-Johan Gyllenstorm was born in 1976 on June 21 in Mölle. Has knowledge in internet marketing with a focus on search engine optimization (SEO). He has expertise in online personal brand strategy and expansion, market analysis, affiliate marketing web automation, extravagant search engine optimization methods. Other relevant knowledge and university studies can be found in the subjects of data analysis and statistics as well as in radiology and image analysis. He got part of his breakthrough when he started his craft company in 2008. Karl-Johan has a patent for the name "Gyllenstorm". Karl-Johan Gyllenstorm has worked as a team base, project manager and site manager in previous professional activities. Gyllenstorm is one of the arms of the House of Knights.
Karl-Johan Gyllenstormś digital books.
Karl-Johan has over 16 years of experience in digital marketing.
The digital marketing journey started in 2008. Karl-Johanś first digital marketing project was a website for his painting business.The website was built in the Joomla system and dominated on relevant Top keywords in the painting industry. He now writes articles about marketing and search engine optimization in the Joomla system and shares his knowledge with the whole world.
Learn more about Karl-Johan Gyllenstorm.
Age: 48
Weight: 106 kg
Length: 188 cm
Shoe Size: 46
Hair color: Brown
Body type: Athletic
Instagram: gyllenstorm_kj
Twitter: gyllenstorm_kj
Medium: kgyllenstorm
 |
Karl-Johan Gyllenstorm is an SEO expert, marketing writer, he is certified in digital marketing by Google Digital Academy 2020. Karl-Johan is also known as “Gyllenstorm.” |
Contact